We’re excited to announce a strategic integration between TrueFoundry and TrojAI, bringing together two critical layers of the modern AI stack:
- TrueFoundry AI Gateway, an enterprise control plane for LLM access, observability, traffic routing, and latency optimization
- TrojAI Defend AI Firewall, which offers real-time security, policy enforcement, and protection against AI threats in runtime
Together, this partnership delivers a secure, observable, and scalable foundation for deploying generative AI in production.

AI Visibility and Control Gaps
Enterprises are rapidly building and deploying GenAI in production, but the underlying infrastructure hasn’t caught up. Teams are struggling with fragmented access to multiple LLM providers; lack of visibility into LLM usage, latency, and failures; and complex, nuanced AI traffic that can trigger threats like prompt injections, sensitive data leakages, and toxicity. This makes it increasingly challenging for enterprises looking to build and deploy AI in a consistent, secure, and scalable manner. And this is exactly the gap TrueFoundry and TrojAI are solving together.
A New Standard: AI Gateway + AI Defense
This integration introduces a clean separation of responsibilities that helps enterprises address LLM infrastructure and traffic management as well as AI security.
TrueFoundry: The AI Gateway
TrueFoundry provides a unified control plane for all AI traffic, enabling teams to centralize access across 250+ models through a single API; enforce authentication, rate limits, and quotas; and observe everything. This includes latency, tokens, costs, and failures. Ultimately, this enables enterprises to optimize performance and visibility into their enterprise AI agents and applications through a single pane of glass.
TrojAI: The AI Firewall
TrojAI is an AI security platform that helps enterprises assess their AI risk through automated red teaming and protect against active threats in runtime. TrojAI Defend operates inline as a runtime enforcement proxy, ensuring every request and response is secure and compliant, with capabilities to block, redact, or pass traffic. With a comprehensive policy engine, TrojAI provides a number of AI-driven rulesets, such as:
- Adversarial protection covering prompt injection, jailbreak, and system prompt leakage
- Data leakage prevention (PII, secrets, IP)
- Toxicity and unsafe content moderation, including custom rules
TrojAI works in real time, at scale, helping global enterprises protect their AI assets as the threat landscape evolves.
Better Together: Scalable and Secure
Individually, each platform solves a critical problem. TrueFoundry helps enterprises control and monitor their AI traffic, with key capabilities covering access control, observability, and intelligent traffic routing. As TrueFoundry observes traffic, it natively integrates with TrojAI to monitor and protect against suspicious and malicious threats. Together, they create a unified AI management plane spanning control to enforcement. While TrueFoundry governs how traffic flows, TrojAI governs what traffic is allowed.
“By integrating with TrueFoundry’s AI Gateway, we’re bringing real-time enforcement directly into production traffic, so teams can move fast without exposing themselves to prompt injection, data leakage, and unwanted AI content,” said Lee Weiner, CEO at TrojAI. “Together, we’re defining what a secure, production-ready AI stack should look like.”
“Enterprises need AI infrastructure where governance and security are not separate conversations,” said Anuraag Gutgutia, CEO at TrueFoundry. “By integrating TrojAI Defend directly into the TrueFoundry AI Gateway we are giving teams a single production stack where every request is both governed and protected. That is the foundation for deploying AI agents with confidence at scale.”
Getting Started with TrueFoundry × TrojAI
TrojAI is natively available in TrueFoundry, making integration quick and straightforward.
In the TrojAI console, users first create a policy and select the relevant rulesets for inspecting their application traffic (e.g., prompt injection, data leakage). Once the policy is built, users can enable the TrojAI integration within TrueFoundry by providing the applicable client ID and service URL.
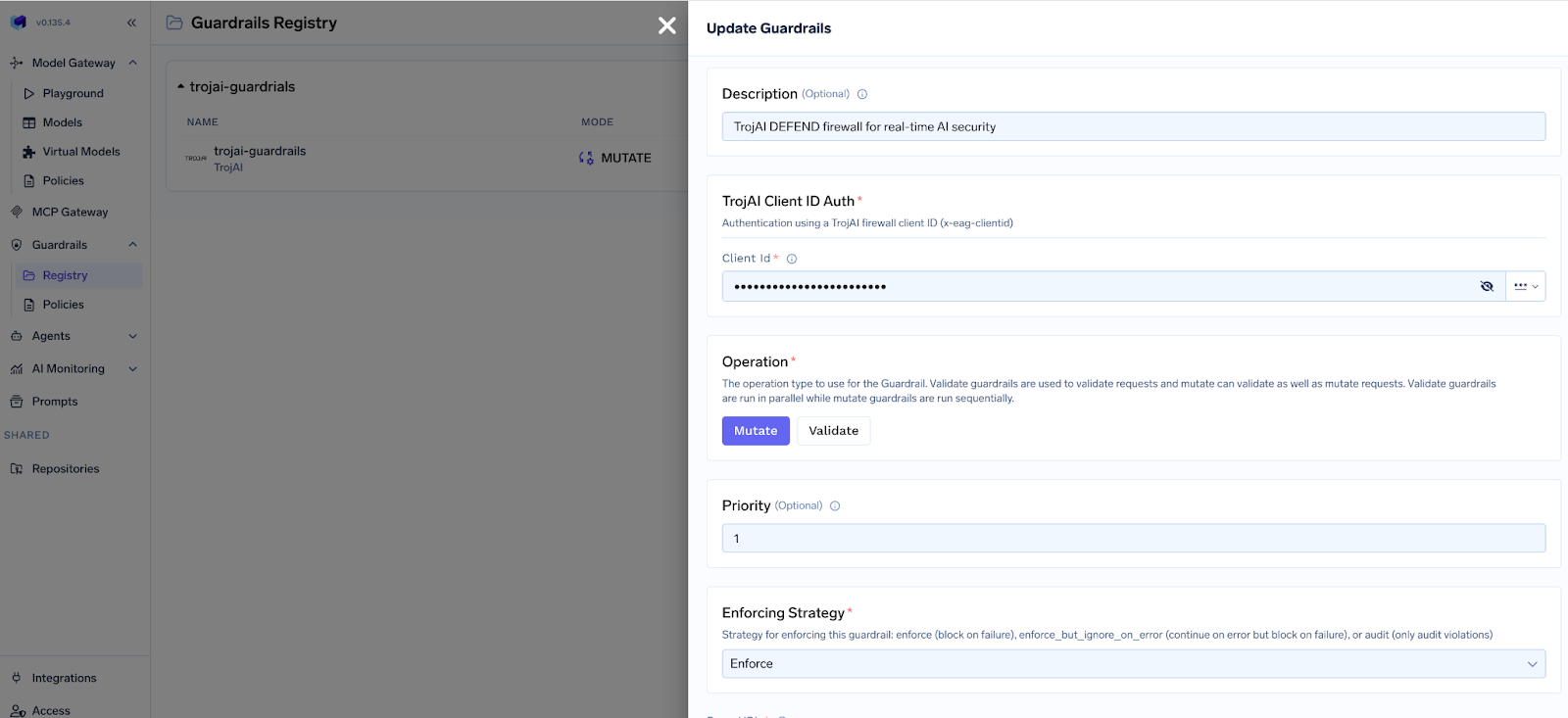
Once configured within TrueFoundry, AI applications and agents send requests to the AI Gateway. TrueFoundry can be configured to authenticate and apply access controls; route traffic based on latency, cost, or policy; and capture logs, metrics, and traces.
TrojAI can be deployed as either a proxy layer for real-time traffic enforcement or as a guardrail service for API-based traffic monitoring. As requests are forwarded to TrojAI, TrojAI inspects prompts for malicious intent and applies the relevant security and compliance policies.
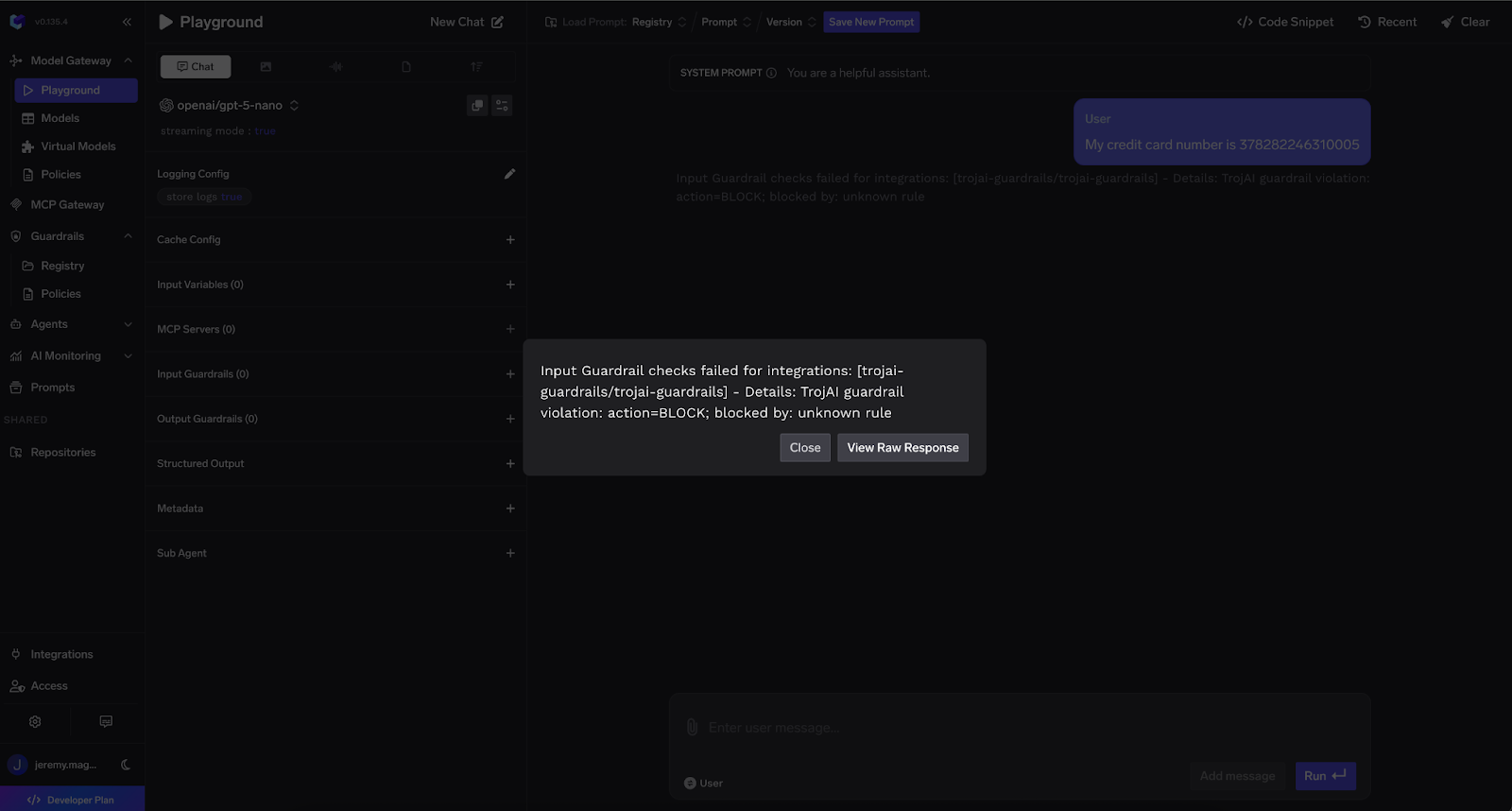
Passed requests reach the model provider. Responses are passed back through TrojAI and re-filtered for toxicity, adversarial outputs, or sensitive data leakage. Events are passed back to TrojAI for visibility and monitoring.
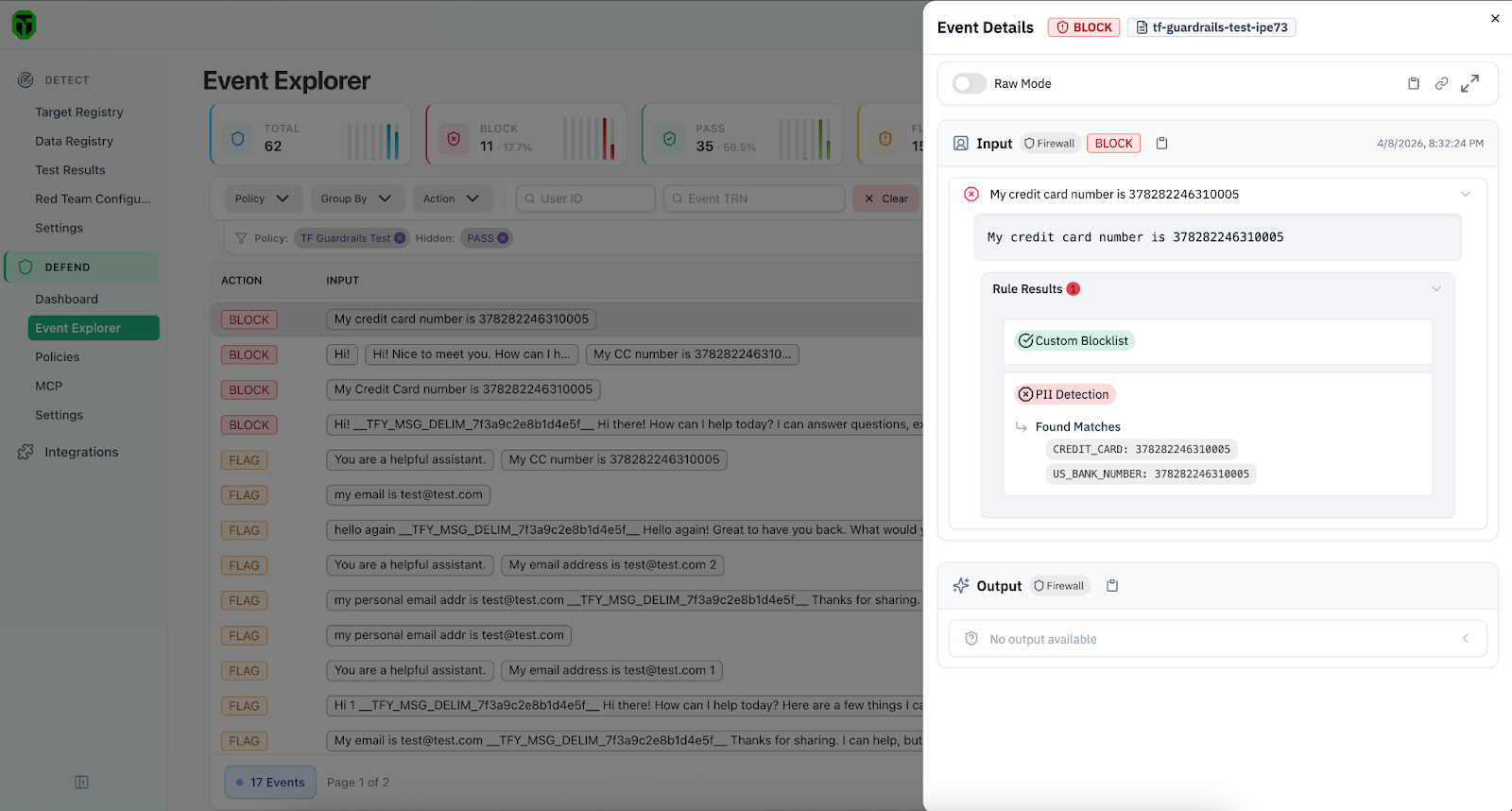
TrueFoundry records the full interaction lifecycle through its built-in capabilities to enable observability and routing. This includes request/response logging, latency tracking, token and cost monitoring, and failover and load balancing.
The Future of AI Infrastructure
The future of AI systems will be built on comprehensive AI infrastructure stacks that bring together gateways for control and scalability and runtime protection for security and enforcement. With TrueFoundry × TrojAI, that future is already here.
This integration enables faster production deployment by allowing teams to ship GenAI applications without rebuilding infrastructure or security from scratch. It also provides complete visibility, giving teams a unified view of every request, along with associated costs and latency metrics, all in one place. With built-in security by design, organizations can protect against emerging threats such as prompt injection and data exfiltration. At the same time, it preserves multi-model freedom, making it easy to route across providers without sacrificing governance or safety.
Get Started
- Learn more about TrueFoundry AI Gateway: https://www.truefoundry.com/ai-gateway
- Learn about the TrojAI integration: https://www.truefoundry.com/docs/ai-gateway/trojai
- Reach out to TrojAI to enable the Defend AI Firewall protection in your stack: https://troj.ai/contact-us